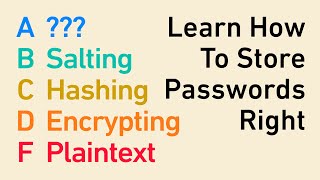
Bcrypt Tutorial in Nodejs | Understand Hashing, Salt, Rainbow Tables and Bcrypt
ฝัง
- เผยแพร่เมื่อ 22 ส.ค. 2024
- What is the safest way to store a user's password in the database? Did you guess hashing? If you did then you would be correct. Hashing with a salt, and using a slow running algo like bcrypt is the safest way to go about storing a user's password in the db. In this video I demonstrate how to use bcryptjs to do just that.
Get 1 on 1 mentorship with me! ▶▶▶calendly.com/c...








no whiteboard , no diagram, no presentation, no animation just code and straight talk at 2x and yes we all understood.Thnak you for such nice explanation
Finally!! Thank You!. I was loosing my mind thinking how bcrypt knows what salt was used when comparing. now I know
Apparently there is also the concept of peppers (a fixed value stored in the server to append to each password) on top of salt. Are there anything else used in the modern day "best practices"?
Can someone explain me how bcrypt works (especially when we are comparing a hash with a text plain password ) ? I dont speak english, i cant undrestand the video
@@dontqsy5101 14:52
Wow, you just explain an entire 2 weeks of my college security course in 17 minutes. Thank you much, sir
This might be the single best programming video on TH-cam...
Love this explanation. Not only you explained the how, but the why. A lot of times we are working with stuff, but we don't really understand the behind the scenes. This explains it in case of what bycript does for us.
This is the first explanation I've heard that I can actually understand. Most of the time people abbreviate the hard parts or give an answer that's too complicated to pick apart. Thanks for the video.
lol was definitely a lot to follow and keep up with but this was exactly what I needed . I wanted to figure out a way to use compare and check the user password and hash password to log a user in but since I love to learn how things work and the process I stumbled upon this video. I got a full understanding how Hashing and Salt works and the answer to my problem. Thank you soooo much !!
Oh man, every single question I had about bcrypt and salts was answered in this video! Really appreciate walking through from bad to best practice and explaining why each step is better than the previous.
Thanks, 14:52 is the explanation I was looking for - the output bcrypt creates contains both the hash and the salt concatenated (plus the number of salting rounds), therefore there is no need to store the salt separately when building an application.
yep, me too!!
Fine job explaining bcrypt! You answered all the burning questions I had about how this works! Thank you and keep sharing!
The best explanation, every single question I had about bcrypt and salts was answered in this video.
Thankyou
Great video! Explained everything I wanted to know. Had to watch at 0.75x speed though cause I couldn't keep up lol
Now this is the best explanation I've gotten on the subject. And you talk fast too. Awesome. I'm subscribing right away
Thanks sir you really explained it well and with every ounce of knowledge. I really appreciate your work and really wish if teachers at my university would have been like you.
You are the real gem we need in this world😍
So basically, Hacker can still get access to the salt and the hashes and figure out the password but he would have to create his own rainbow table for that specific salt which would be infeasible for him. Thankyou for the explanation!!
Fantastic explanation, especially on the comparing of existing hashes which is the part I was confused about. Thank you!
last part is video is what i was looking for. Awesome explanation! ! !
Thank you for actually explaining what it is!
Pleasure
Hey !! what a amazing viedo !!! Really man, that was full of knowledge ...Thanks
this so amazing you deserve a lot of suscribers
Had to hit the like and subscribe button.
This was masterfully done.
Thank you very much.
Awesome, Awesome explanation! Clarified everything. Exactly what i was looking for!!! Thanks!!
Awesome video! Clear explanation! Thank you so much
Don't know how to thank you for this video.
Glad it helped
Only thing I don't understand is why we even bother with the salt if we append it to the hashed password and then store it in the DB... is it because the hackers won't know the length of the salt? Or is it because any random salt at all makes the rainbow table useless? Regardless, very good tutorial. You explain things well.
Best explanation I have yet seen.
היי
תודה לך
ממש מגניב שמצאתי את הערוץ שלך
thank you so much
it's very useful
Excellent explanation thanks a ton!
Exactly, I had this question in my mind, thank you for answering
Explained very well with no BS thanks
Really well explained. Great video, thanks 🙏
Good explanation. Thanks!
excellent video, got rid off all my doubts
Well explained, Chaim so good :)
Sir really thanks for explaining this
Iam shocked this video only has 2k views !
Great explanation, just loved it
Well done - great video
Awesome, Awesome explanation! Clarified everything. Thanks!!
You are most welcome!
u r a gr8 teacher
Very helpful explanation. Thank You!
excellent presentation. very clarifying what happens when someone forgets their password?
Amazing explanation . Thank you so much!
Amazing Stuff!!
stat from 13:30 for the comparing scenario
great content man...
Excellent explanation!
Thanks a lot for this.
Hello, this is the only video that i got to understand bcrpyt. thank you for that. i have a question. does this mean i'll have to pull the hash from the database then compare it back in nodeJS?
correct
thanks for this great video. I have a couple of questions. Is the salt also stored in the database somewhere? Or is it always some fixed length, say n, and the comparison is made without the last n characters in the hash with the salt? In other words, how is the salt removed? Also why do the salts in this video always start with a$10$?
14:52 Thank you!!!
thanks for really interesting video Chaim!
You’re welcome!
Great explanation. Thank you
Great explanation! But talking a bit slower would make it even more perfect ;)
Thanksalot sir!
Incredible.
Amazing explanation, thank you sir
You’re most welcome!
This may be stupid question, but if the salt that has been used is stored in the DB why can't the hackers just use that information to run through the common passwords. Is this unavoidable and this is just a way to make it more time comsuming for the hackers?
Thank you so much for this video, my 80% confusion is clear now but I am still having doubts about the hacker's technique, can't they use the same bcrypt method and apply their RANMBOW thing on it while logging in? but many things are clear with your video thanks a lot:)
Very complete, clear and answered all of my questions. Exemplary video. If I may, why did you opt for bcryptjs over bcrypt? For the lack of dependencies?
Thank you! Honestly I cant remember the exact reason why I chose the js version here in this video, but typically in a real project, going with the JS version does make things simpler. I had an instance where I was trying to deploy code to AWS lambda with the non JS version and it was giving me major issues.
@@CodingWithChaim I’ll go for the js version then ahah, thanks again! Have a nice day :] (you got a new sub btw)
Thank you! Welcome to the channel
Thanks!
You mentioned while comparing the password bcrypt take the salt out from the hash stored in the database and attaches it to the password that user has entered and then creates the hash for comparing both the has one present in the database and one that user has entered, but how does bcrypt know what is the start index and the end index of the salt to get the salt out of the hash i.e. stored in the database.
Bcrypt is the one that appends the salt to the hash so they know where it is
Thank you
you are amazing
thanks
On point
in just 17 mins i got a cyber security degree, lol jk i don't think its this simple XD.
Thank you.
So if I get it right if the hacker knows where the salt begins and where it ends (since bcrypt is an open source package) we're back to the initial spot where they can just use the rainbow tables again, right?
No because the salt is totally random and is hashed.
@@CodingWithChaim but we can see on bcrypt repo that the salt has 16 chars and that the stored password will be the sequence of salt+password so the hacker doesnt need to "crack" the salt hash, they just need to take it off. Am I missurderstanding something?
@@alexsinx the salt gets added to the user’s password and then the combined string gets hashed. This means the resulting hash will not show up in a rainbow table
Seems reasonable to me too. If a hacker knows the hash() function and salt, he still can create rainbow tables.
It should look like this:
rainbow table = "salt "+ hash( "salt" + "popular_password")
But hacker need to create a new table for every "salt".
bcrypt should be used in the frontend and then the hash should pass through network and stored in the db right?
No. The password is sent in plain text to the server and then hashed on the server.
So theoretically, if a hacker got access to your database, couldn't they make a rainbow table out of the normal passwords hashed with the first 27 characters of your stored password (aka your salt)? Or is the idea that that takes so long that it isn't feasible?
It's practically infeasible to go back to the value from a cryptographic hash
Lechaim
I am completly dizzy !
😳
you really speak very fast
Speaking very fast
Andrew Tate must have learned from him.
bro you talk faster than eminem. Calm down please.
you talk too much
Awesome, Awesome explanation! Clarified everything. Thanks!!
You are most welcome!